
The widespread use of computers and internet makes computer security an increasingly important problem. Homeland security has also become the top prority of our nation. One basic approach to the security problem is to analyze large data collected from all possible sources. The results of the analysis can help spot suspecious activities and track down known malicious intents. We have been studying how visualization can supplement traditional data analysis methods, which often fail to handle the scale and complexity of the security data. Our work is largely driven by computer network security but our research results are also applicable to general data analysis and knowledge discovery. We have developed several prototype systems to demonstrate the effectiveness of visualization based analysis and searching.
Research Team
Kwan-Liu Ma, Professor, IDAV and Department of Computer ScienceS. Felix Wu, Associate Professor, Department of Computer Science
Christopher Muelder, PhD student
Michael Ogawa, PhD student
Previous members:
Jonathan McPherson, MicrosoftSoon Tee Teoh, San Jose State University
Research Highlights
 |
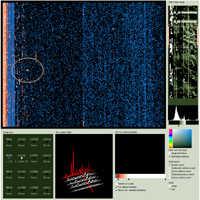
ScanVis |
|
 |
Information Visualization |
|
 |
Elisha |
|
 |
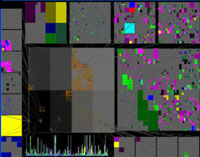
PortVis |
|
 |
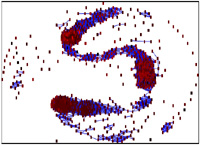
PaintingClass |
Education
- ECS272, Information Visualization, Winter 2005
- ECS163 Information Interfaces, Spring 2005
Publications
- A Visualization Methodlogy for Characterization of Network Scans,
Chris Muelder, Kwan-Liu Ma, and Tony Bartoletti,
to appear in Proceedings of VizSEC 2005, October 26, 2005.
[pdf]
- Interactive Visualization for Network and Port Scan Detection,
Chris Muelder, Kwan-Liu Ma, and Tony Bartoletti,
to appear in Proceedings of RAID 2005, September7-9, 2005.
[pdf]
- Performing BGP Experiments on a Semi-realistic Internt Testbed Envrionment,
Ke Zhang, Soon Tee Teoh,
Shih Ming Tzeng, Pattapon Limprasittipom, Kwan-Liu Ma,
S. Felix Wu, Chen-Nee Chuah,
to appear in Proceedings of the 3rd International Workshop on Security in Distributed
Computing Systems, June 2005.
- Discovering Parametric Clusters in Small World Graphs,
Jonathan McPherson, Kwan-Liu Ma, Michael Ogawa,
in Proceedings of ACM Symposium on Applied Computing, March 13-17, 2005.
[pdf]
- PortVis: A Tool for Port-Based Detection of Security Events,
Jonathan McPherson, Kwan-Liu Ma, Paul Krystosek, Tony Bartoletti, Marvin Christensen. In Proceedings of CCS Workshop on Visualization and Data Mining for Computer Security, ACM Conference on Computer and Communications Security, October 29, 2004.
[pdf]
- Combining Visual and Automated Data Mining for Near-Real-Time Anomaly Detection and Analysis in BGP, Soon Tee Teoh, Ke Zhang, Shih Ming Tseng, Kwan-Liu Ma, and Felix Wu. In Proceedings of CCS Workshop on Visualization and Data Mining for Computer Security, ACM Conference on Computer and Communications Security, October 29, 2004.
[pdf]
- Visual Data Analysis for Detecting Flaws and Intruders in Computer Network Systems,
Soon Tee Teoh, TJ Jankun-Kelly, Kwan-Liu Ma, and Felix Wu. IEEE Computer Graphics and Applications, special issue on Visual Analytics, 24(5), September/October 2004, pp. 27-35.
[pdf]
- Visual-based Anomaly Detection for BGP Origin AS Change Events,
Soon Tee Teoh, Kwan-Liu Ma, and S. Felix Wu,
in Proceedings of the 14th IFIP/IEEE Workshop on Distributed Systems: Operations and Management, October 20-22.
[pdf]
- Visualization Techniques for Internet Routing Data,
Soon Tee Teoh, Kwan-Liu Ma, and S. Felix Wu,
in Proceedings of the IEEE Visualization 2003 Conference, October 20-24.
[pdf]
-
PaintingClass: Interactive Construction, Visualization and Exploration of Decision Trees, Soon Tee Teoh and Kwan-Liu Ma,
in Proceedings of ACM KDD 2003 Conference, August 24-27.
[pdf]
- StarClass: Interactive Visual Classification Using Star Coordinates,
Soon Tee Teoh and Kwan-Liu Ma,
in Proceedings of the 3rd SIAM International Conference on Data Mining,
May 1-3, 2003, pp. 178-185.
[pdf]
- Case Study: Interactive Visualization for Internet Security,
Soon Tee Teoh, Kwan-Liu Ma, and S. Felix Wu,
in Proceedings of the IEEE Visualization 2002 Conference.
[pdf]
Others
- One for All, InfoVis 2004 Poster, Soon Tee Teoh.
- Summarizing Network Traffics with Information Visualization, LLNL Student Symposium Poster, Chris Muelder, August 12, 2004.
- PaintingClass: Interactive Construction, Visualization and Exploration of Decision Trees,
InfoVis 2003 Poster, Soon Tee Teoh.
Current research projects are sponsored by NSF ITR, DOE LLNL and Boeing.